For many years we used the build castle analogy to secure your environments. Is it time for a change?

In today’s world, where we have malicious actors attacking your datacenters every minute of the day with various attacks from Malware to Ransomware, to name a few, we need to protect and detect these acts before they cause harm.
NSX-T 3.2 needs to be a vital part of protecting and responding to attacks from malicious actors.
Let’s start with the outer haul of your cargo ship, your perimeter security. The haul has physical security, of course, and communication, a.k.a network security that uses a next-generation firewall (NGFW) that secures data transmission.
Special Note: Drawings are simplified

There are many techniques used to build this haul that we can cover later. Let’s stay with the analogy, keep it super simple (KISS) and add some floors to this ship. My thought process is to use hardware-based NGFW to control communication/traffic flows between the floors. Wait, I thought this was a blog on protection with NSX-T 3.2; rest assured, we are getting there. KISS right? You will not change or rebuild floors of your ship very often, if ever, so let’s create zones( AKA floors) where security enforcement at hardware-based NGFW.
Special Note: When it comes to mixing HW and SW with various protect techniques, you want to KISS and gain the advantage of looking at traffic in multiple ways and giving flexibility in protecting your most valuable assets.
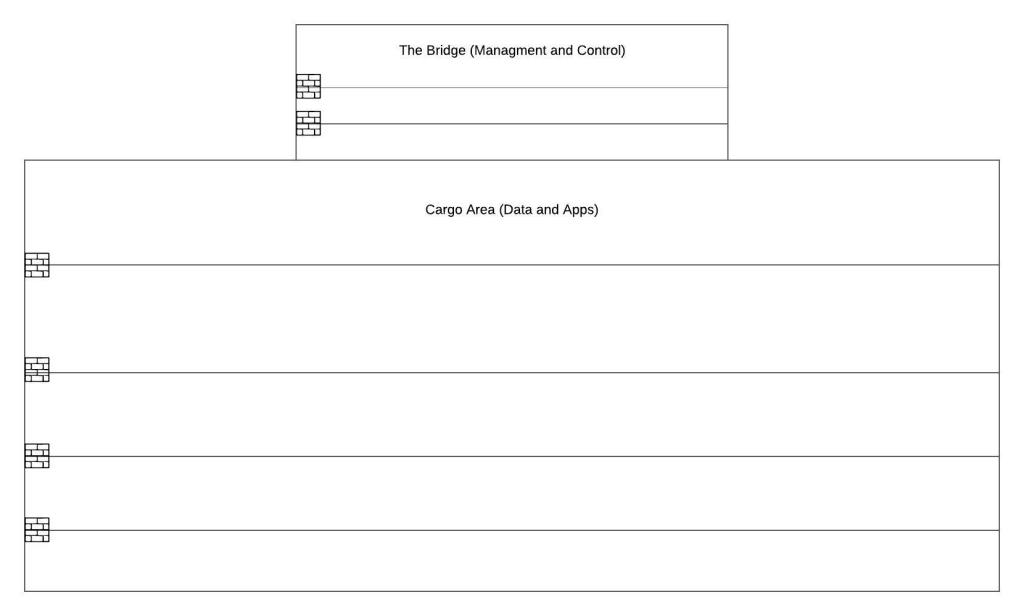
Now let’s introduce NSX-T 3.2, which brings the control points closer to the applications (AKA Cargo) where you can configure or reconfigure cargo holds. Let’s think about that for a minute, the ability through automation and manual software changes can change behavior and control points. I am now thinking about Network as a Service (NaaS) or Security as a service (SecaaS). We can create a new cargo configuration in test and development before applying it to production.
With the distributed model expanding beyond Distributed Fire Walls (DFW) or Internal Segmentation Firewalls (ISFW) are now Distributed Next-Generation Firewalls (DNGFW). With the integrations from the Lastline acquisition, NSX-T 3.2 can provide distributed Advanced Threat Prevention (ATP) with malware prevention for known and zero-day malware. Distributed behavioral IDS looking for pattern matches and other anomalous traffic.
Ok, let that sync in for min; let’s talk about more distributed goodness! Network Traffic Analysis to see lateral movement anomalies. Network Detection and Response (NDR) to help provide relief from alert overload with MITRE ATT&CK visualize campaign view.
You end up with a cargo ship with disturbed security to protect and detect malicious attackers. Look at all those reconfigurable doors and control points I have negative now as a malicious attacker.

We have covered one way to protect with NSX-T; we touched on detect. We will dive deeper into detecting using telemetry and management tools soon. We will also cover using Carbon Black to respond and different recovery strategies. Stay tuned to hear more about VMware Security or reach out and ask how VMware can help secure your business.