Defending the VCF 9.1 Core: Virtual Patching, IDPS, and Surviving the “Mythos” Era of AI Threats
Executive Summary: The Speed of the Adversary Has Changed
In early April 2026, the cybersecurity landscape experienced a tectonic shift. Anthropic announced Project Glasswing and the restricted release of Claude Mythos Preview. This wasn’t just another language model; it was a demonstration of autonomous, AI-driven offensive cyber capabilities. We saw reports of models autonomously discovering zero-day vulnerabilities in mature codebases and—as highlighted by the recent Cloudflare incidents—chaining seemingly minor, low-severity bugs into devastating, multi-step exploits.
The human-driven vulnerability lifecycle (discovery, weaponization, patching) has been compressed from months to hours.
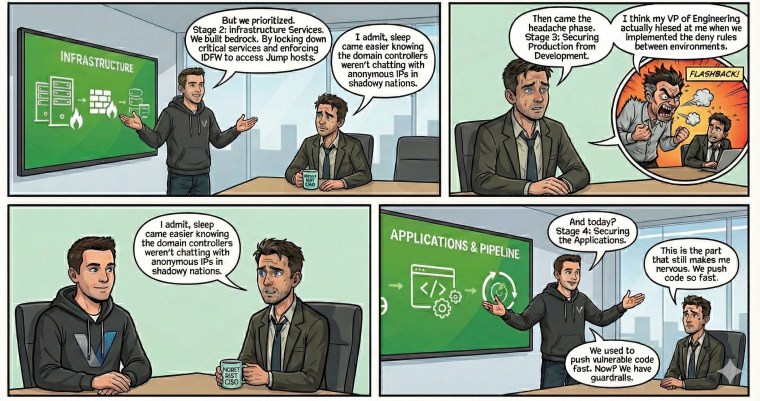
In my previous posts, we discussed how VMware Cloud Foundation (VCF) 9.1 introduces System Security Profiles and Turbo Mode to secure Agentic AI workflows. Today, we need to turn those same defensive weapons inward. How do we protect the “keys to the kingdom”—the VCF 9.1 Management Domain and critical Infrastructure Services—against an adversary that operates at machine speed? The answer lies in strict adherence to NIST frameworks and the aggressive application of vDefend Distributed Firewall (DFW) 1-2-3-4 methodology and Intrusion Detection/Prevention Systems (IDPS) for Virtual Patching.
The New Threat Landscape: Why Legacy Defenses Fail
The capabilities demonstrated by Mythos-class AI models render perimeter-only defenses entirely obsolete. Academic research is rapidly catching up to this reality. Recent evaluations demonstrate that Large Language Models (LLMs) are becoming highly proficient at solving complex Capture the Flag (CTF) offensive security challenges, mimicking real-world cyber threats at scale (Shao et al., 2024).
Furthermore, as organizations deploy advanced multi-agent systems, they introduce novel risks—such as systemic mis-coordination, collusion, and highly complex destabilizing dynamics—that we are only just beginning to understand (Hammond et al., 2025). Attackers are also bypassing traditional AI alignment and safety guardrails by employing multi-turn jailbreaks that distribute malicious intent across seemingly benign query sequences (Asl et al., 2025). Even the protocols designed to standardize AI tool usage, such as the Model Context Protocol (MCP), are creating vast new attack surfaces characterized by namespace typo-squatting, tool poisoning, and supply chain compromise (Hou et al., 2025).
When an AI can autonomously map a network, discover a zero-day in your DNS server, and execute a multi-stage payload in under 24 hours, traditional patching cycles are a death sentence.
Securing the VCF 9.1 Management Domain (NIST 800-207)
The VCF Management Domain houses vCenter Server, SDDC Manager, and the NSX Managers. If an attacker breaches this domain, they own the hypervisor fabric.
Applying Zero Trust (NIST SP 800-207): NIST 800-207 mandates that “all communication is secured regardless of network location.” We can no longer treat the Management VLAN as a trusted zone. By defining identity-based Security Groups (sg-), we can create a tight perimeter around these components.
Example: VCF Management Domain DFW Ruleset
| Rule Name | Source (Group/Tag) | Destination (Group/Tag) | Service/Ports | Action | NIST 800-207 Alignment |
|---|---|---|---|---|---|
| Allow-Admin-Access | sg-admin-jumpboxes | sg-vcf-management | HTTPS (443), SSH (22) | ALLOW | Explicit, verified access for authorized admins only. |
| Allow-ESXi-to-vCenter | sg-esxi-hosts | sg-vcenter | UDP 902, HTTPS (443) | ALLOW | Least-privilege agent heartbeat and management traffic. |
| Allow-SDDC-Mgmt | sg-sddc-manager | sg-esxi-hosts, sg-vcenter | API, SSH (22) | ALLOW | Enables SDDC Manager lifecycle and automation workflows. |
| Mgmt-Lockdown | ANY | sg-vcf-management | ANY | DROP | Default Deny – Eliminates implicit trust to the core. |
- Micro-Segmentation via DFW: In VCF 9.1, we use the vDefend Distributed Firewall to enforce a “default deny” posture within the Management Domain, as demonstrated in the “Mgmt-Lockdown” rule above.
- Identity-Based Security Groups: We move away from static IPs. By tagging management components, the DFW policy moves with the workload, ensuring that if a vCenter appliance is restored or migrated, its strict security perimeter remains intact.
Shielding Infrastructure Services (NIST 800-82 R3)
Infrastructure Services—Active Directory (AD), DNS, NTP, and DHCP—are the nervous system of your data center. In Operational Technology (OT) and enterprise environments alike, these are prime targets for AI-driven reconnaissance and lateral movement.
Aligning with NIST SP 800-82 R3 (Boundary Protection): NIST 800-82 R3 emphasizes the need for strict network segmentation and boundary protection for critical systems.
- DNS & NTP Isolation: These services should reside in a heavily restricted infrastructure tier. A compromised DNS server allows an attacker to manipulate traffic routing for the entire SDDC. We must enforce NIST 800-53 SC-7 (Boundary Protection) by using the DFW to restrict DNS traffic strictly to UDP/TCP 53, and only from designated internal subnets.
- The “Any-Any” Trap: AI models look for overly permissive rules. Using vDefend Rule Analysts (RA) that is part of Security Intelligence we must map the baseline traffic of our AD and DNS servers and eliminate any shadowed or redundant “Allow Any” rules.
The Lifeline: Virtual Patching with vDefend IDPS
This is where VCF 9.1 truly shines against the Mythos-class threat. When a new vulnerability drops (or an AI discovers a zero-day that gets leaked), it takes time for vendors to release a patch, and even longer for infrastructure teams to schedule a maintenance window.
What is Virtual Patching? Virtual Patching utilizes the vDefend IDPS (Intrusion Detection/Prevention System) to inspect traffic for the specific exploit signatures of a vulnerability, blocking the attack before it reaches the unpatched application.
Example: Critical Management Domain IDPS Signatures
| Target Component | CVE / Signature ID | Vulnerability Description | vDefend Action | NIST 800-53 R5 |
|---|---|---|---|---|
| Aria Operations | CVE-2026-22719 (Sig 1150806) | Command Injection during product migration leading to RCE. | Reject / Drop | SI-3 (Malicious Code Protection) |
| vCenter Server | CVE-2024-37079 (Sig 1140021) | DCERPC protocol Heap-overflow leading to Remote Code Execution. | Reject / Drop | SI-3, SC-7 (Boundary Protection) |
| ESXi Hosts | CVE-2025-22224 (Sig 1150999) | Hypervisor escape / Sandbox breakout from compromised VM. | Reject / Drop | SI-4 (Information System Monitoring) |
| Web UI / Agents | CVE-2026-39365 (Sig 4105305) | Path Traversal attacks in Vite Servers used by AI frontends. | Reject / Drop | SI-10 (Information Input Validation) |
How it works in VCF 9.1:
- Hypervisor-Level Enforcement: The IDPS engine sits directly at the vNIC of the VM. Traffic doesn’t need to be hairpin-routed to a physical appliance.
- Turbo Mode Acceleration: With VCF 9.1’s Turbo Mode utilizing SCRX acceleration, we can run deep packet inspection (DPI) and IDPS at up to 9 Gbps per host. This means we can aggressively inspect traffic hitting our DNS, AD, and vCenter servers without crushing performance.
- Dynamic Threat Intelligence: VMware’s Threat Intelligence cloud pushes updated signatures continuously, enabling zero-day defense before official vendor patches can be fully tested and deployed.
NIST 800-53 R5 Alignment:
- SI-3 (Malicious Code Protection): IDPS drops payloads attempting to execute remote code on management appliances (like the vCenter DCERPC exploit).
- SI-4 (Information System Monitoring): The IDPS feeds alerts directly into the vDefend NDR console, providing your SOC with immediate visibility if an AI-driven attack is attempting to probe your infrastructure services.
Conclusion: Matching Machine Speed
The release of models like Claude Mythos Preview through Project Glasswing signifies a permanent escalation in cyber warfare. The attacker is no longer a human manually typing commands; it is an autonomous system iterating through exploit chains at machine speed.
To survive, our defenses must also operate at the infrastructure level. By combining the strict Zero Trust micro-segmentation of the vDefend DFW with the high-performance Virtual Patching capabilities of the VCF 9.1 IDPS, we transition from a reactive patching cycle to a proactive, defensible architecture. In the age of AI threats, the network itself must become the immune system.
What’s Your Defense Strategy?
Are you ready to turn your network into an immune system? I’d love to hear how your teams are adapting to these AI-driven threats.
- Join the conversation: Drop a comment below on your experience with vDefend IDPS or your zero-trust journey. What challenges are you facing with virtual patching?
- Need a customized blueprint? Reach out to VMware by Broadcom Account Team to discuss how VMware PSO can help you design and deploy a defensible VCF 9.1 architecture.
- Stay ahead of the curve: Subscribe now so you never miss a deep dive into VMware security, NIST compliance, and my ongoing vDefend DFW journey!
References
Asl, J. R., Narula, S., Ghasemigol, M., Blanco, E., & Takabi, D. (2025). NEXUS: Network Exploration for eXploiting Unsafe Sequences in Multi-Turn LLM Jailbreaks. arXiv. https://doi.org/10.48550/arxiv.2510.03417 Cited by: 6
Hammond, L., Chan, A., Clifton, J., et al. (2025). Multi-Agent Risks from Advanced AI. arXiv. https://doi.org/10.48550/arxiv.2502.14143 Cited by: 170
Hou, X., Zhao, Y., Wang, S., & Wang, H. (2025). Model Context Protocol (MCP): Landscape, Security Threats, and Future Research Directions. arXiv. https://doi.org/10.48550/arxiv.2503.23278 Cited by: 540
Shao, M., Jancheska, S., Udeshi, M., et al. (2024). NYU CTF Bench: A Scalable Open-Source Benchmark Dataset for Evaluating LLMs in Offensive Security. arXiv. https://doi.org/10.48550/arxiv.2406.05590 Cited by: 30